
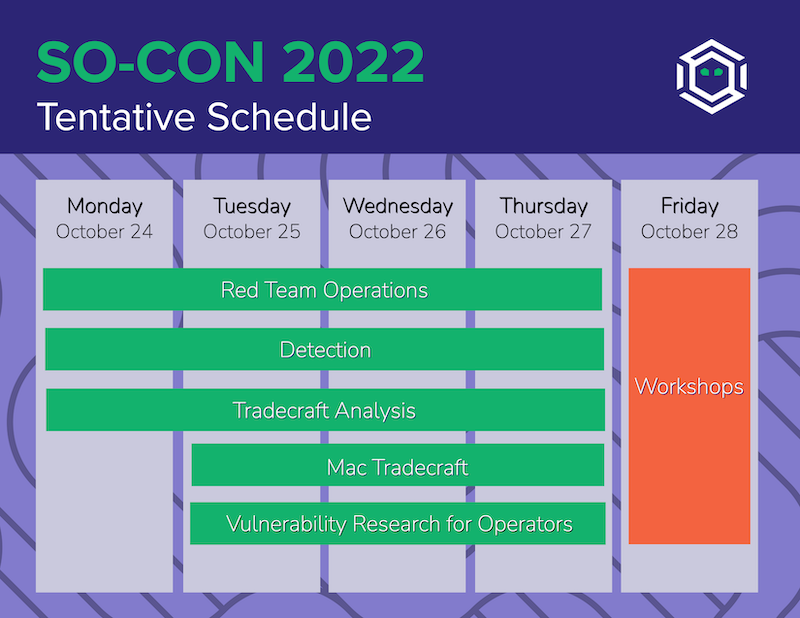
SpecterOps is pleased to announce SO-CON 2022, our third-annual training event taking place online October 24th – 28th, 2022. In addition to hosting all five of our Adversary Tactics training courses, including newly expanded, three-day versions of our Mac Tradecraft and Vulnerability Research for Operators courses, SO-CON will wrap the week with a series of new training workshops developed by our team of Specters.
Join us in October and let’s keep learning – together!

SO-CON 2022 kicks off the week with our Adversary Tactics courses:
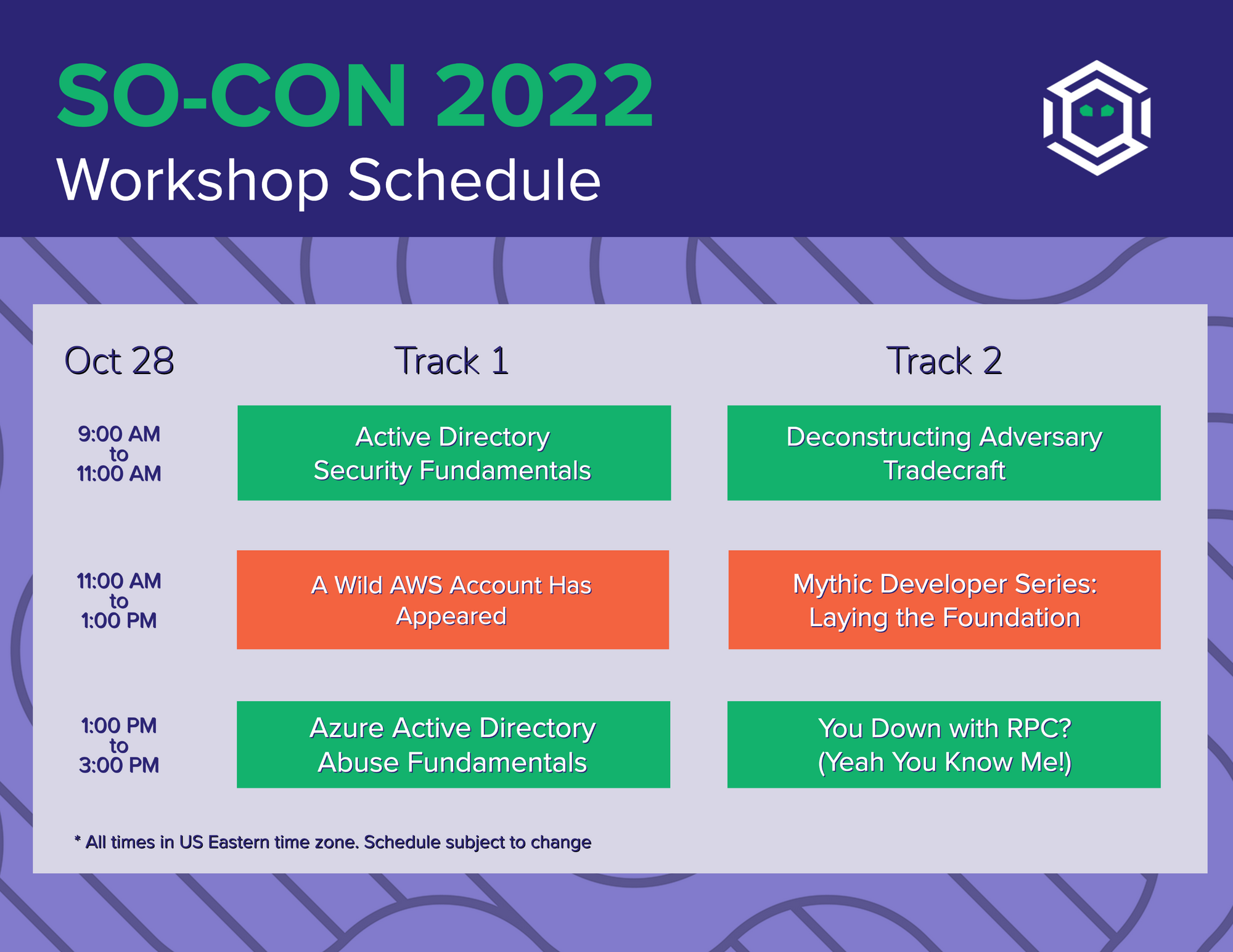
SO-CON Workshops will wrap up the week with a series of new workshops delivered online throughout Friday. Workshops will focus on simulation and detection concepts, mindsets, and operational techniques and tooling. Workshop details can be found below!
We're delivering the following six workshops as part of our SO-CON training event:
Attendees for all of our SO-CON training courses can register for the workshops for free.
All other attendees can purchase a ticket. All proceeds from these workshops will be donated to the Equal Justice Initiative.
Workshops will be run in two tracks throughout the day. If you'd like to attend multiple workshops, please note the schedule in this listing below to ensure their times don't conflict. See below for a full schedule of workshops.
Presented by: Carlo Alcantara
Description: This workshop is designed to teach foundational basics of Active Directory from a security perspective and give hands on experience with industry standard tools. Organizations today face many challenges related to securing Active Directory and developing an effective security program and maintaining a hardened security posture can often prove difficult in determining where to start, how to identify and triage misconfigurations, and how to proactively prevent future misconfiguration and degradation of Active Directory. A regular security audit or penetration test is just the first step in effectively securing your environment with the next and equally as important phase of triage and remediation. Understanding the fundamentals of what causes misconfiguration in Active Directory will help your organization take a proactive approach in identifying and remediating vulnerabilities before they become, costly, embedded in process, and lead to degradation of the environment.
Format: Remote online
Day/Time: Friday, October 28, 2022; 9:00 - 11:00 AM ET
Track: 1
Duration: 2 hours
Presented by: Daniel Heinsen
Description: Gaining access to an AWS environment on a red team engagement can be very different than accessing AWS externally. This workshop will be an introductory AWS course targeted towards red teamers who encounter AWS environments during an assessment but aren’t quite sure how to take full advantage of that access. While the material is not comprehensive, it is designed to give red teamers the crash course necessary to enable them to effectively access and analyze any AWS environment they happen to stumble upon.
Format: Remote online
Day/Time: Friday, October 28, 2022; 11:00 AM - 1:00 PM ET
Track: 1
Duration: 2 hours
Presented by: Andy Robbins & Jonas Bülow Knudsen
Description: This workshop will equip you with the fundamental knowledge and skills you need to simulate an adversary operating with an Azure Active Directory tenant. In two hours you will learn about the mechanisms that control AzureAD identity and access management, OAuth token usage and juggling, and how to use open source tools to simulate adversary actions. Students will use those skills to execute an attack path in an AzureAD lab environment.
Format: Remote online
Day/Time: Friday, October 28, 2022; 1:00 - 3:00 PM ET
Track: 1
Duration: 2 hours
Presented by: Jared Atkinson
Description: Detection is a complex problem. There are eternal questions that we can't seem to answer fully. What types of behaviors should I be searching for? How do I know a behavior when I see it? What even is a behavior? How do I know that my detection rule is comprehensive? The difficulty with complex problems is that many known and unknown variables exist, and we cannot control them enough to simplify the problem. One of my favorite principles is called "Better Wrong than Vague." It states that "the solution to any sufficiently complex problem necessarily requires the use of assumptions, whether explicitly or implicitly, and it is better to make assumptions explicitly because then the assumptions can be criticized and potentially falsified." With this principle in mind, we must strive to understand the system as much as we can.
This workshop guides attendees through analyzing an attack technique to understand how it functions, what variables exist for attackers to take advantage of, and propose a framework through which defenders can view this complex system. We will then transition from understanding the attack to understanding our ability to perceive activity within the information domain which will allow us to convert our knowledge of these variables into a base-level detection. This workshop is for you if you want to move beyond attacker tools to understand how attack techniques work under the hood and how you can use this knowledge to build comprehensive detections and measure coverage.
Format: Remote online
Day/Time: Friday, October 28, 2022; 9:00 - 11:00 AM ET
Track: 2
Duration: 2 hours
Presented by: Cody Thomas
Description: Do you have awesome ideas for command and control agents, C2 profiles, or new techniques? Do you want to see your visions realized without having to do all the tedious work of creating a user interface or defining an API? Then this workshop is for you! In this two-hour workshop we'll cover a hands-on, in-depth example of setting up a development environment and create the necessary components for a Mythic C2 agent and custom C2 profile.
This workshop focuses on the Mythic side of agent development and how everything connects together rather than diving into the complexities of the agent code itself. Mythic utilizes Docker and Docker-compose for easy deployment and sharing of agents; however, this workshop will show you how to locally create and test agent code with Mythic without the need to convert your agent to Docker. Mythic's message format uses JSON, but that might not be the easiest for every language (especially lower level languages); we will run through an example of creating and setting up a translation container to allow completely custom agent message formats and cryptography. Finally, we'll go through the process of crafting a custom C2 profile.
Format: Remote online
Day/Time: Friday, October 28, 2022; 11:00 AM - 1:00 PM ET
Track: 2
Duration: 2 hours
Presented by: Duane Michael & Evan McBroom
Description: With the recent popularity of Windows RPC abuse in the offensive security community, we've observed a gap in foundational training on RPC. Join us for this workshop where you will learn the fundamentals of RPC and then apply them to write your own RPC server and client in C++. Participants will learn how to define an interface, initialize and register a server, and build a client to authenticate and interact with it.
Format: Remote online
Day/Time: Friday, October 28, 2022; 1:00 - 3:00 PM ET
Track: 2
Duration: 2 hours






We launched a charity shirt drive for SO-CON featuring three designs. Orders can be made from now until the drive ends on October 28th.
All proceeds benefit the Equal Justice Initiative! Snag some ghostly swag and help a great cause!
Updated: September 30, 2022
Back To Announcements